Nobody plans to build an IT graveyard.
It just… happens.
A few retired laptops get stacked in a closet. A monitor leans against a wall in facilities. Somebody in accounting still has an old dock. A branch office has a pile of devices from a refresh nobody fully reconciled. A remote employee swears they sent their laptop back, and maybe they did, maybe it is sitting in a box somewhere between “handled” and “forgotten forever.”
That mess is exactly why the ITAD process matters.
Not because “disposition” is a trendy acronym. Not because every old device is a five-alarm legal emergency. Because once equipment leaves active use, you need a real process for what happens next. Not a vibe. Not a hopeful email chain. A process.
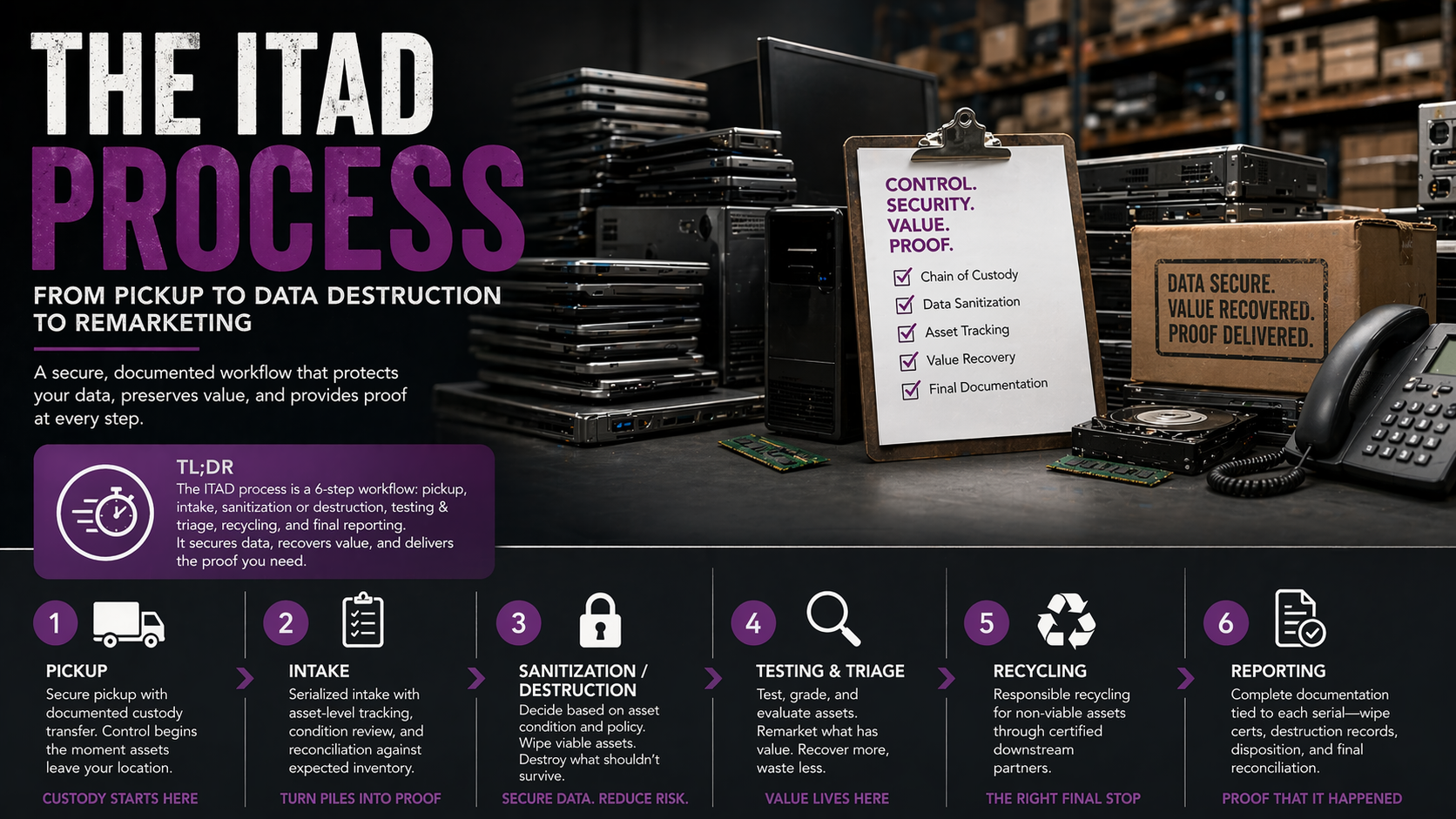
At its core, the ITAD process is the structured path retired business technology follows from pickup, to intake, to sanitization, to resale, destruction, or recycling, all with documentation that proves what happened. When that process is tight, you reduce risk, preserve recovery value, and stop old equipment from becoming a weird mix of clutter, liability, and silent budget loss.
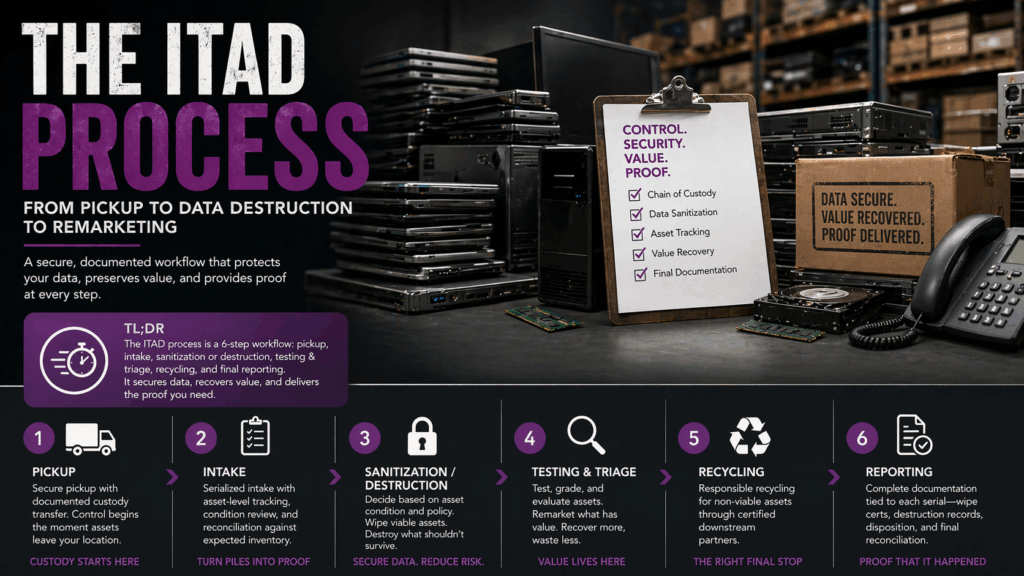
TL;DR
The quick version of the ITAD process.
The ITAD process starts before data destruction. It starts the moment retired equipment is identified for removal. From there, the strongest programs move through pickup, chain of custody, intake, serial tracking, sanitization, testing, remarketing, destruction where needed, recycling where appropriate, and final reporting. Good process protects data, but it also protects value. If equipment is still viable, validated wiping can keep it in play for resale instead of sending money straight into a shred bin. If it is not viable, the process should still end with clear proof, not guesswork.
What the ITAD process actually includes
A lot of people picture ITAD as one moment.
Truck shows up. Stuff goes away. Drives get destroyed. Done.
That is not really the process. That is the middle of the movie, and half the plot is missing.
A real ITAD process includes asset identification, secure handoff, serialized intake, data sanitization or destruction, asset evaluation, resale where it makes sense, recycling where it does not, and final documentation. Each step matters because each step answers a different question.
What did you have?
Where did it go?
Was the data actually sanitized?
Did the asset still have value?
What proof do you have now?
Miss one of those and the process starts to wobble.
That is why secure IT asset disposition is never just about “getting rid of equipment.” It is about controlling the handoff, the handling, and the outcome from beginning to end.
Step 1: Pickup is where control begins
A lot of companies think security starts when a device gets wiped.
Nope. Security starts when custody changes hands.
The minute a retired asset leaves your office, your branch, your storage room, or your remote employee’s home, the process is already underway. If that handoff is sloppy, the rest of the chain is compromised before intake even begins.
That is why pickup is not just a transportation detail. It is the first control point.
Whether equipment moves through scheduled pickup or a structured shipping workflow, the point is the same, retired assets should not drift through the world like mystery luggage. They should enter the process in a way that ties them to an expected inventory, a real handoff, and a documented path forward.
This sounds obvious until you see how many organizations still rely on ad hoc movement. Somebody from IT grabs a stack. A facilities person sends a pallet. Devices show up later with partial notes, vague counts, and the technological equivalent of “trust me, bro.”
That is how blind spots get born.
Step 2: Intake is where the pile becomes a process
Once equipment arrives, the next job is turning “a pile of stuff” into actual tracked assets.
That means serial capture. Asset-level intake. Condition review. Reconciliation against expected inventory. The boring stuff, in other words… the stuff that saves you later.
Because here is the truth nobody loves hearing. If intake is weak, everything after it gets weaker. Wipe logs matter less if you cannot confidently tie them back to the correct serials. Destruction certificates matter less if the inventory going in was muddy. Recovery value gets fuzzier. Audit readiness gets shakier. Confidence starts sliding.
This is where a lot of internal processes break down, especially with endpoints. Servers in a data center tend to get respect. Laptops, monitors, tablets, docks, phones, and branch-office leftovers get chaos. You can dive deeper on ITAD for Corporate Devices here.
Endpoint-heavy environments are where sloppy tracking turns into real headaches, because the assets are distributed, inconsistent, and easy to lose control of if nobody tightens the process early enough.
And once control slips, it gets expensive fast.
Step 3: Sanitization or destruction, the decision point that actually matters
This is the part everybody jumps to, and fair enough. It is the sexy part. The dramatic part. The part with the words “data destruction” in it.
But even here, the smartest ITAD process is not brute force. It is decision-making.
Some assets should be securely wiped. Some should be physically destroyed. Some should be evaluated first, then pushed down one path or the other based on condition, policy, media type, and recovery potential.
That distinction matters because the wrong choice can cost you twice. Once in risk, once in lost value.
When validated data erasure makes sense
If a device is still viable, validated data erasure is often the better path.
Why? Because wiping protects the data without automatically killing the asset’s resale potential. That means the device can still move into remarketing if it passes inspection and fits the right recovery channel. Suddenly what looked like a disposal event becomes a value-recovery event. Not magic. Just process.
That is why this step needs more than a factory reset and a thumbs-up. It needs a real ITAD data erasure solution, something validated, documented, and aligned with the level of security the asset requires. Which is exactly why the question Are Blancco Wipes Really Compliant? matters. A compliant wipe is not about crossing your fingers and hoping a delete button did something noble. It is about validation, proof, and whether the sanitization method stands up to scrutiny after the fact.
When destruction is the right move
Destruction still absolutely belongs in the ITAD process.
Failed drives, damaged media, devices that do not pass wipe validation, assets governed by stricter internal policy, all of those may need physical destruction. That is not a failure of the process. That is the process doing its job.
The mistake is treating destruction like the only safe option for every device.
Destroy too much and you kill recovery value you did not need to kill. Destroy too little and you leave unnecessary exposure in the system. The right answer is triage, not theatrics.
And yes, standards matter here. NIST SP 800-88 Rev. 2 is the current federal guidance for media sanitization, and it matters because it reinforces a simple but important truth: sanitization is not one blunt action applied to everything the same way. The right method depends on the media, the risk, and the required outcome.
Step 4: Testing, triage, and remarketing
This is the step a lot of competitors underplay because it is less dramatic than shredding, but this is where a surprising amount of business value lives.
Not every retired device belongs in the scrap stream.
Some should be destroyed. Some are truly end-of-life. But plenty of assets still have market value if they are handled properly. That means they can be tested, evaluated, wiped, and moved into remarketing channels instead of being treated like worthless debris.
That is not a minor side benefit. It can materially change the economics of a refresh.
We dug into that in Stop the Bleed: The True Value of IT Asset Recovery & Buyback, because too many companies lose money in slow motion. They let viable devices sit in closets, branch offices, and storage rooms until depreciation does the dirty work for them. By the time action happens, the risk is still there, but the value is gone.
That is a rough trade.
A tighter ITAD process cuts against that. It moves faster, makes the wipe-or-destroy decision earlier, and preserves remarketing opportunities where the asset still deserves one.
Step 5: Recycling is the end of the road, not the whole road
This is where a lot of conversations get lazy.
People say “recycling” when they really mean “the entire retirement process,” and those are not the same thing.
Recycling matters. Of course it does. Non-viable, obsolete, or physically destroyed assets still need a responsible downstream path. But recycling is the finish for certain assets, not the definition of ITAD itself.
The full process comes first. Identification. Custody. Intake. Sanitization. Triage. Remarketing or destruction. Then recycling for what is truly done.
That order matters because it forces better decisions. It keeps companies from tossing recoverable equipment into the same category as dead scrap. It also keeps the security side from turning into loose assumptions and half-complete records.
Step 6: Reporting is where the whole thing becomes real
This is the final step, and in a weird way, it is also the whole point.
Because without reporting, the process is just a story you are telling yourself.
Final reporting is where each asset’s path gets tied together, serial tracking, wipe results, destruction records where applicable, resale outcomes, recycling documentation, and reconciliation back to the original inventory. This is the part that turns a handled project into a provable one.
And this is where weak vendors start to feel very weak.
A nice-looking summary is not enough. Generic certificates are not enough. Broad claims are not enough. If the documentation cannot stand up to internal questions later, then you are still carrying more uncertainty than you think.
That is why a real ITAD service should feel controlled all the way through, not just at the flashy moments. Pickup should feel controlled. Intake should feel controlled. Sanitization should feel controlled. Reporting should feel controlled. If one step feels improvised, that is usually not an isolated problem.
Where ITAD processes usually fall apart
Not at the wipe bench. Usually earlier.
They fall apart when assets move before anyone tightens custody. They fall apart when expected inventory and actual intake do not match. They fall apart when endpoints are scattered across branches, remote users, and storage closets nobody wants to own. They fall apart when companies sit on viable equipment too long and let recovery value leak out month by month. They fall apart when somebody decides a spreadsheet with questionable serials counts as documentation.
And they fall apart when everyone treats the project like a disposal event instead of an operational workflow.
That last one is the killer.
Because once you start thinking about ITAD as a real process, the priorities get clearer. Control early. Track tightly. Sanitize with proof. Recover value where you can. Destroy what should not survive. Recycle what is truly at end of life. Document all of it.
Final answer: the ITAD process is really about control
The ITAD process is the controlled retirement workflow for business technology.
It starts at pickup, not destruction. It moves through intake, tracking, sanitization, evaluation, and final disposition. It ends with remarketing, destruction, or recycling, plus the documentation to prove the right thing happened to the right asset at the right time.
That is the real answer.
Not “haul it away.”
Not “wipe it later.”
Not “we should probably deal with that pile someday.”
A strong ITAD process gives you security, accountability, and a better shot at recovering value before old equipment becomes nothing more than a problem with dust on it.

Frequently Asked Questions: The ITAD Process
Direct answers to the most common questions about IT asset disposition workflows, data sanitization, and hardware retirement processes.
What is the ITAD process?
The ITAD process is the structured workflow for retiring business technology securely. It includes six key steps: (1) pickup with documented custody transfer, (2) serialized intake and asset tracking, (3) data sanitization or physical destruction based on asset condition and policy, (4) testing and triage for remarketing potential, (5) recycling for end-of-life materials, and (6) final reporting with proof tied to each serial number. This process protects data, preserves recovery value, and provides audit-ready documentation.
What are the steps in the ITAD process?
The ITAD process follows six sequential steps: Step 1 – Pickup and custody transfer with documented handoff. Step 2 – Intake with serial capture, condition review, and inventory reconciliation. Step 3 – Sanitization decision (data erasure vs. physical destruction) based on asset viability and policy. Step 4 – Testing, triage, and evaluation for remarketing opportunities. Step 5 – Recycling for non-viable assets through certified downstream channels. Step 6 – Reporting with serial-matched documentation, sanitization certificates, and audit trail.
When does the ITAD process actually start?
The ITAD process starts the moment retired equipment is identified for removal—not when it gets wiped or destroyed. Security begins when custody changes hands. The pickup phase is the first control point where assets should be tied to expected inventory, documented handoff procedures, and a clear chain of custody. Waiting until devices arrive at a processing facility means the process has already been compromised if the handoff was sloppy.
What happens during ITAD intake?
ITAD intake transforms untracked equipment into documented assets. This includes: capturing serial numbers for every device, conducting asset-level condition assessments, reconciling received inventory against expected lists, and identifying discrepancies before processing begins. Weak intake undermines everything that follows—wipe logs can’t be tied to correct serials, destruction certificates lose accuracy, and audit readiness collapses. Strong intake is where control begins.
What is the difference between data erasure and data destruction in ITAD?
Data erasure (wiping) uses software to overwrite data on functional drives, allowing the device to be reused or resold while protecting information security. Physical destruction uses shredding, crushing, or degaussing to make drives permanently unreadable, typically for failed media, damaged devices, or assets under strict disposal policies. The choice depends on asset condition, data classification, recovery value, and compliance requirements. Validated erasure preserves resale value; destruction is final but eliminates all recovery potential.
Can you recover value from retired IT equipment through the ITAD process?
Yes. Viable equipment that passes testing and receives validated data erasure can move into remarketing channels instead of destruction. Recent-generation laptops, workstations, networking equipment, and functional peripherals often retain significant resale value. A disciplined ITAD process identifies recovery opportunities early through proper triage, preserves value through validated wiping instead of unnecessary destruction, and converts disposal costs into budget offsets. Equipment that sits in storage loses value monthly while risk persists.
What documentation should the ITAD process produce?
Complete ITAD documentation includes: serialized intake records showing what was received, chain of custody logs documenting every handoff, sanitization certificates with method/timestamp/operator tied to specific serials, destruction certificates for physically destroyed assets, resale or recycling records showing final disposition, and reconciliation reports matching outcomes back to original inventory. Generic batch certificates or summary reports without serial-level detail fail audit requirements.
What is NIST SP 800-88 and why does it matter for ITAD?
NIST SP 800-88 Rev. 2 is the federal standard for media sanitization. It defines three sanitization methods: Clear (overwriting for reuse), Purge (more aggressive methods for sensitive data), and Destroy (physical destruction). The standard emphasizes that sanitization method must match media type, data classification, and risk level—not a one-size-fits-all approach. Organizations following NIST guidance can demonstrate compliance through documented, appropriate sanitization decisions rather than defaulting to destruction for all assets.
Where do ITAD processes typically fail?
ITAD processes fail at custody transfer (assets moving before documentation), weak intake (inventory mismatches and missing serials), endpoint distribution (laptops and peripherals scattered across branches and remote workers), delayed action (letting viable equipment lose value in storage), inadequate documentation (spreadsheets instead of serial-matched certificates), and treating disposition as a one-time event instead of a repeatable operational workflow.
Is recycling the same thing as ITAD?
No. Recycling is one possible outcome of the ITAD process, not the process itself. ITAD covers the complete workflow: pickup, intake, sanitization, triage, destruction, remarketing, and recycling. Recycling handles end-of-life material streams for non-viable assets. Calling everything “recycling” causes companies to skip triage, miss recovery opportunities, and treat all retired equipment as worthless scrap instead of making asset-specific decisions about wiping, reselling, destroying, or recycling.
How long does the ITAD process take?
The ITAD process timeline depends on volume, geography, and asset complexity. Typical workflows: pickup scheduling (1-2 weeks for multi-site coordination), intake and serialization (1-3 days for batch processing), sanitization and testing (2-5 days depending on method and volume), triage and remarketing evaluation (1-2 weeks), and final reporting (delivered within 1-2 weeks post-completion). Delays usually come from weak intake documentation, scattered endpoint locations, or unclear custody at pickup.
What should I look for in an ITAD process provider?
Strong ITAD providers demonstrate: documented chain of custody from pickup through final disposition, serialized intake with asset-level tracking, validated data sanitization (not just factory resets), serial-matched wipe or destruction certificates, transparent triage process for value recovery, R2 or e-Stewards certification showing third-party auditing, multi-site pickup coordination capabilities, and complete audit packets with method/timestamp/operator documentation. Ask to see sample reporting before committing.
Why is chain of custody important in the ITAD process?
Chain of custody proves who had the asset, when they had it, and what happened during each phase. It creates an unbroken audit trail from pickup through final disposition that can withstand regulatory scrutiny, internal audits, and data breach investigations. Without documented chain of custody, you can’t prove assets were handled securely, connect sanitization certificates to specific devices, or demonstrate compliance with data protection requirements. Gaps in custody create liability.
How does the ITAD process handle endpoints vs. data center equipment?
Endpoints (laptops, monitors, docks, tablets, phones) require more complex ITAD processes than data center equipment because they’re distributed across offices, branches, and remote workers. Endpoint ITAD needs: coordinated multi-site pickups, ship-kit programs for remote returns, peripheral tracking (items easily forgotten), partial-inventory reconciliation (not everything comes back), and consumer-grade remarketing channels. Data center equipment benefits from centralized location, consistent tracking, and enterprise resale channels. Both need validated sanitization and documentation.