You know the pile.
A few retired laptops in a closet. Monitors leaning against a wall. Old docks, phones, maybe a printer nobody wants to touch. A branch office has a stack of devices in a back room. A remote employee still has a company laptop from two refresh cycles ago. Somebody says, “We should probably deal with that,” and then everybody goes back to doing literally anything else.
That pile is where ITAD starts.
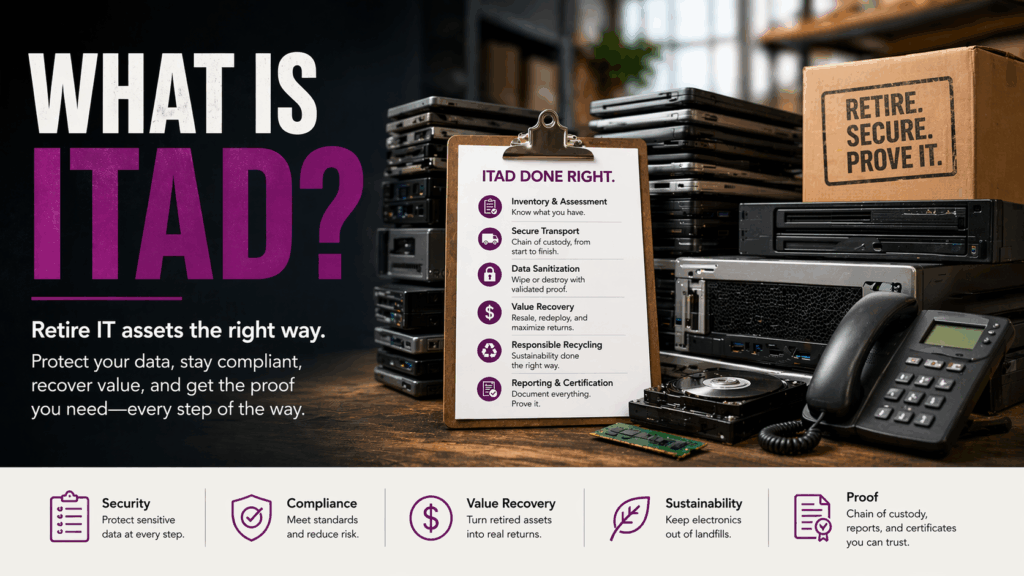
ITAD stands for IT asset disposition. In plain English, it is the process of retiring business technology in a way that protects your data, documents what happened, and helps you decide what should be wiped, resold, destroyed, or recycled. It is not just “getting rid of old gear.” It is controlled retirement with proof. On our side, that means itemized tracking, chain of custody, certificates, and handling that is built to stand up when somebody from compliance, finance, or leadership asks the annoying follow-up question… “Can you prove it?”
TL;DR: What is ITAD?
If you only need the fast version, here it is.
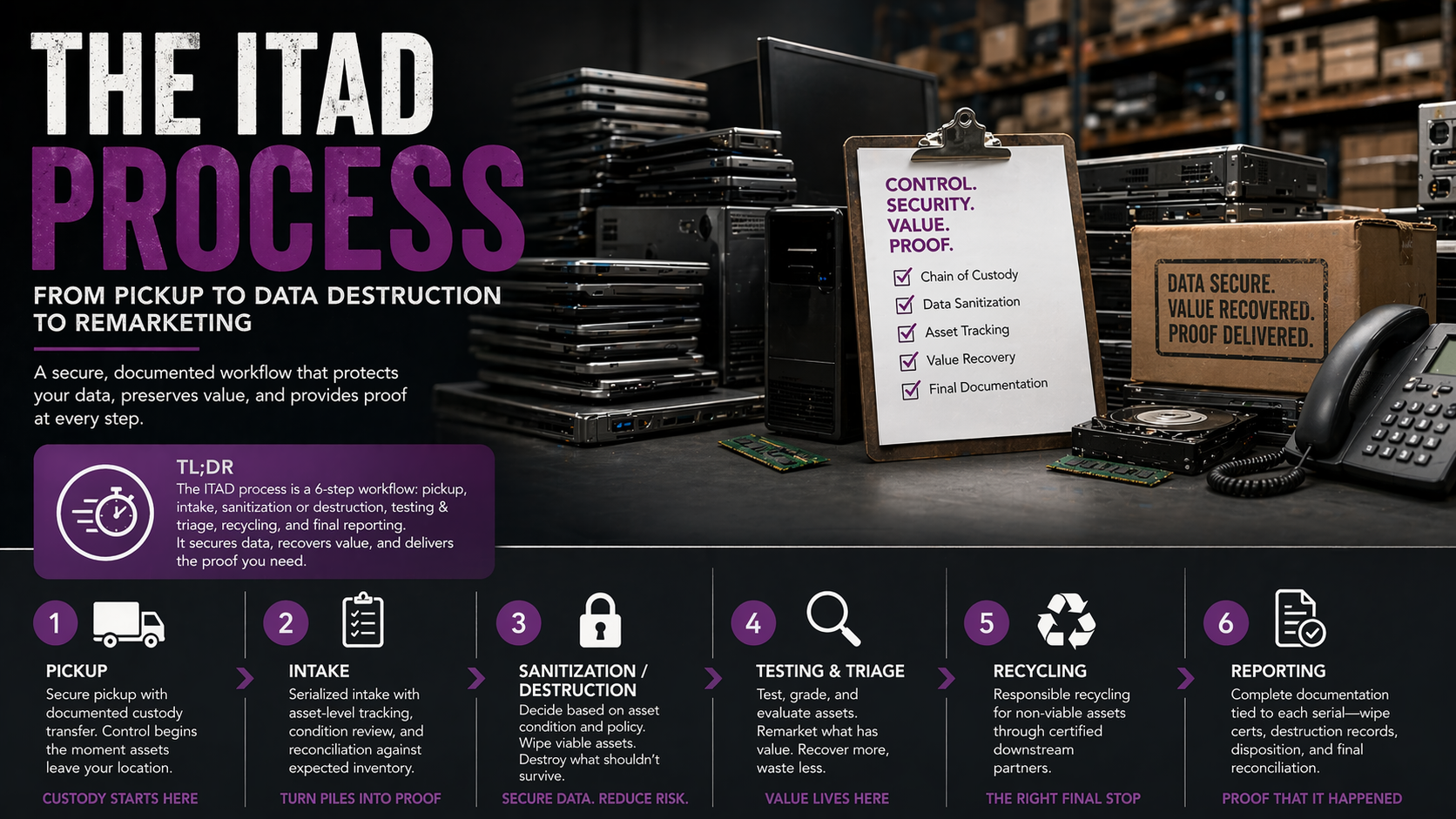
ITAD is the structured process of retiring business devices securely. It usually includes inventory capture, transport, chain of custody, data sanitization, resale evaluation, destruction where needed, recycling, and final reporting. A real process is built to answer five things without guessing: what you had, where it went, whether the data was actually sanitized, what still had value, and what documentation exists afterward. That is why strong programs are not just about disposal, they are about security, accountability, and recovering value when the equipment still has life left in it.
What does ITAD stand for?
ITAD stands for IT asset disposition.
That sounds dry. Fair enough. Most acronyms do.
But the word that matters is disposition. Not disposal. Not junk removal. Not “take this stuff away before the office move.” Disposition means making the right decision for each asset. Some devices should be securely wiped and resold. Some should be redeployed. Some should be physically destroyed. Some should go to downstream recycling. The job is not to treat every retired device like a dead microwave. The job is to choose the right path, then prove it happened. NIST’s current guidance, SP 800-88 Rev. 2, describes media sanitization as a process that renders access to target data infeasible for a given level of effort, and frames that work inside a formal sanitization program tied to the sensitivity of the information.
That is also why ITAD is not the same thing as e-waste recycling. Recycling can be one outcome. It is not the whole process.
What ITAD actually includes
A real ITAD program starts before the truck shows up.
First, you need to know what you actually have. That means serials, asset lists, device types, condition, and whether the equipment is centralized or scattered across offices, branches, storage rooms, and home offices. From there, the process moves into custody, transport, intake, sanitization, testing, resale evaluation, destruction where needed, recycling where appropriate, and final documentation. We build that around itemized asset tracking, chain-of-custody documentation, and records that can be matched back to real devices, not vague summary sheets with a nice logo at the top.
This is where a lot of companies get tripped up. They think the hard part is disposal. It usually is not. The hard part is control.
Because the mess is rarely sitting in one neat room waiting politely for pickup. The mess is distributed. It is the laptop that never made it back from a remote employee. The monitor graveyard in facilities. The network gear from a branch refresh. The “temporary” pile that becomes permanent because nobody wants to own it. We see that constantly, which is why we wrote End-of-Life IT Asset Disposition for Corporate End-User Devices. End-user assets are decentralized, inconsistently tracked, and easy to mishandle right when security and recovery value matter most.
Why ITAD is not just recycling
This is one of the biggest misunderstandings in the category.
If your plan is “find a recycler and hope for the best,” that is not really an ITAD strategy. That is outsourcing your anxiety.
Recycling deals with end-of-life material streams. ITAD deals with the business process that comes before that, what the device is, whether it still works, whether the data has been sanitized, whether it holds resale value, whether it needs destruction, and what proof you will have at the end. Sometimes recycling is the correct finish. Sometimes resale is. Sometimes destruction is. The point is that you do not know the right answer until the asset is handled inside a proper process. That is why our certified ITAD services are built around compliance, chain of custody, itemized tracking, and data destruction that meets recognized standards, not generic “electronics removal” talk.
Wiping vs. destruction, this is where the money lives
This is the section most people care about, even if they pretend they do not.
Because yes, destruction matters. But wiping is where a lot of the business value gets saved.
If equipment is still viable, validated wiping can preserve its path to resale or redeployment. That changes the economics completely. What looked like a disposal cost starts turning into value recovery. Instead of paying to make useful assets disappear, you can pull money back out of your refresh cycle and take some of the sting out of new equipment purchases. That is a big deal, especially when you are cycling through large fleets of endpoints, printers, servers, or mixed business hardware. We broke that down in Stop the Bleed: The True Value of IT Asset Recovery & Buyback, because too many companies are still treating recoverable hardware like worthless junk.
And yes, this is where Blancco comes into the conversation. If a device can be securely sanitized and validated, wiping keeps the door open for resale. So, are Blancco wipes really compliant? That is the right question. Not “did someone hit delete,” not “did we factory reset it,” not “do we think it is probably okay.” The right question is whether the wipe was validated, documented, and aligned with the level of security the asset actually requires. That is the difference between a real process and a hopeful shrug.
Now, on the other side of that coin, destruction still absolutely belongs in ITAD. Failed media, damaged drives, assets that do not pass wipe validation, and equipment that falls under stricter internal policy may need physical destruction. That is not a contradiction. That is responsible triage. Wipe what should be wiped. Destroy what should be destroyed. Document both. Move on. Our secure data destruction approach is built around exactly that kind of decision-making, not one blunt rule applied to every device in the pile.
Why companies use ITAD in the first place
Security is the obvious answer, but it is not the only one.
Yes, retired devices can hold customer data, employee records, internal files, financial information, and a whole lot of things you do not want floating around after the device leaves your building. That alone is enough reason to take retirement seriously. But strong ITAD programs also solve for proof, logistics, and money.
Proof matters because nobody wants to defend a weak paper trail after the fact. “We think it got recycled” is not documentation. “Our vendor said they handled it” is not documentation. If it is not tied back to serials, validated reports, and final records, it is not much of a defense at all. That is why we push hard on chain of custody, itemized asset tracking, and documentation that is actually usable when someone asks for it later. Our banking-focused writeup says it plainly, if it’s not provable, it doesn’t exist. That sounds harsh. It is also true. We dig into that in ITAD Solutions for Banks: How to Turn Cycles Into Budget Offsets, but the principle applies far beyond banking.
Then there is the budget side. Old equipment loses value while it sits. Closets are not neutral. Storage rooms are not neutral. Delay is not neutral. Every month that viable equipment sits untouched, you are often losing recovery value while keeping the risk. That is a brutal combo.
The endpoint problem nobody wants to own
Data centers get the dramatic language. Endpoints usually get the headaches.
Laptops, monitors, docks, tablets, printers, phones, those are often the assets that drift. They move between people, departments, branch offices, and home offices. Tracking gets messy. Ownership gets fuzzy. Then refresh time comes around, and suddenly nobody is fully sure what is still out there, what came back, what was wiped, and what still has value.
That is not rare. That is normal.
Which is why ITAD for endpoint-heavy organizations has to be a process, not a cleanup day. If your retirement workflow breaks the second a device leaves headquarters, you do not really have a workflow. You have wishful thinking with a spreadsheet.
Local logistics matter more than people think
Even when you run a national program, the real world still shows up with loading docks, building rules, freight elevators, branch schedules, and the kind of chaos that never seems to make it into neat vendor one-pagers.
That is exactly why white-glove execution matters in markets like Greater Boston. Pickup is not just pickup when you are coordinating access, serial capture, chain of custody, and secure movement out of dense offices and mixed facilities. In our Boston ITAD Guide: White-Glove Pickup, Secure Data Destruction, and Asset Recovery (Without the Headaches) we talk about this pretty bluntly, because what looks like a disposal issue on the surface is usually a documentation issue, a logistics issue, and a value-recovery issue all piled into one.
So, what is ITAD?
ITAD is the controlled retirement of business technology.
It is the process of figuring out what you have, securing it, sanitizing it properly, recovering value when that makes sense, destroying what should not survive, recycling what is truly at end of life, and documenting the whole thing so you are not left guessing later.
That is the real answer.
Not “take it away.”
Not “throw it in e-waste.”
Not “we will deal with it after the move.”
A real ITAD company should help you reduce risk, keep the paper trail clean, and stop bleeding value out of equipment that still has a second life left in it. And if your current process cannot prove what happened to each asset… then that is not really a process yet. It is just a pile with a deadline.
FAQ | What is ITAD?
Common questions about IT asset disposition, data security, and hardware retirement.
What does ITAD stand for?
ITAD stands for IT asset disposition. It refers to the process of retiring business technology in a secure, documented way, whether that means wiping, reselling, destroying, or recycling the equipment.
What is IT asset disposition?
IT asset disposition is the structured handling of retired IT equipment after it leaves active service. That can include inventory tracking, chain of custody, data sanitization, resale evaluation, physical destruction, recycling, and final reporting.
Is ITAD the same as e-waste recycling?
No. E-waste recycling can be one part of ITAD, but it is not the whole thing. ITAD also includes data security, documentation, asset tracking, and decisions around resale, redeployment, destruction, or recycling.
Why is ITAD important for businesses?
ITAD helps businesses reduce data security risk, maintain a cleaner audit trail, and recover value from viable retired equipment. Without a real process, old devices can turn into a mix of liability, clutter, and lost money.
What types of equipment go through ITAD?
Common ITAD assets include laptops, desktops, servers, monitors, docking stations, printers, tablets, mobile devices, networking equipment, and other business electronics that have reached end of life or are being replaced.
Is wiping better than physical destruction?
Not always. It depends on the condition of the asset, the sensitivity of the data, and internal policy. If equipment is still viable, validated wiping can preserve resale value. If media is damaged, fails wipe validation, or requires a stricter disposition path, physical destruction may be the right move.
Can companies recover value through ITAD?
Yes, sometimes. If equipment is still functional and can be securely sanitized, it may be resold or remarketed. That recovery value can help offset part of the cost of a hardware refresh instead of turning the whole project into a pure disposal expense.
What should a business look for in an ITAD provider?
A strong ITAD provider should be able to show clear chain of custody, itemized asset tracking, validated wipe reporting, certificates when destruction is needed, and final documentation tied back to actual devices.
Does ITAD only apply to large enterprises?
No. Large enterprises often have bigger refresh cycles and more logistics to manage, but mid-sized businesses, multi-site companies, healthcare groups, banks, schools, and growing organizations can all benefit from a documented ITAD process.
What is the difference between deleting data and secure sanitization?
Deleting files or doing a factory reset is not the same as validated data sanitization. Secure sanitization is designed to make the data inaccessible using a documented method that aligns with the security level the asset actually requires.